The recent cyberattack involving Canvas by Instructure is rapidly becoming one of the most significant education-sector cybersecurity incidents of 2026. What began as a breach involving a third-party learning management system has now impacted universities and colleges across the United States, including institutions in Colorado.
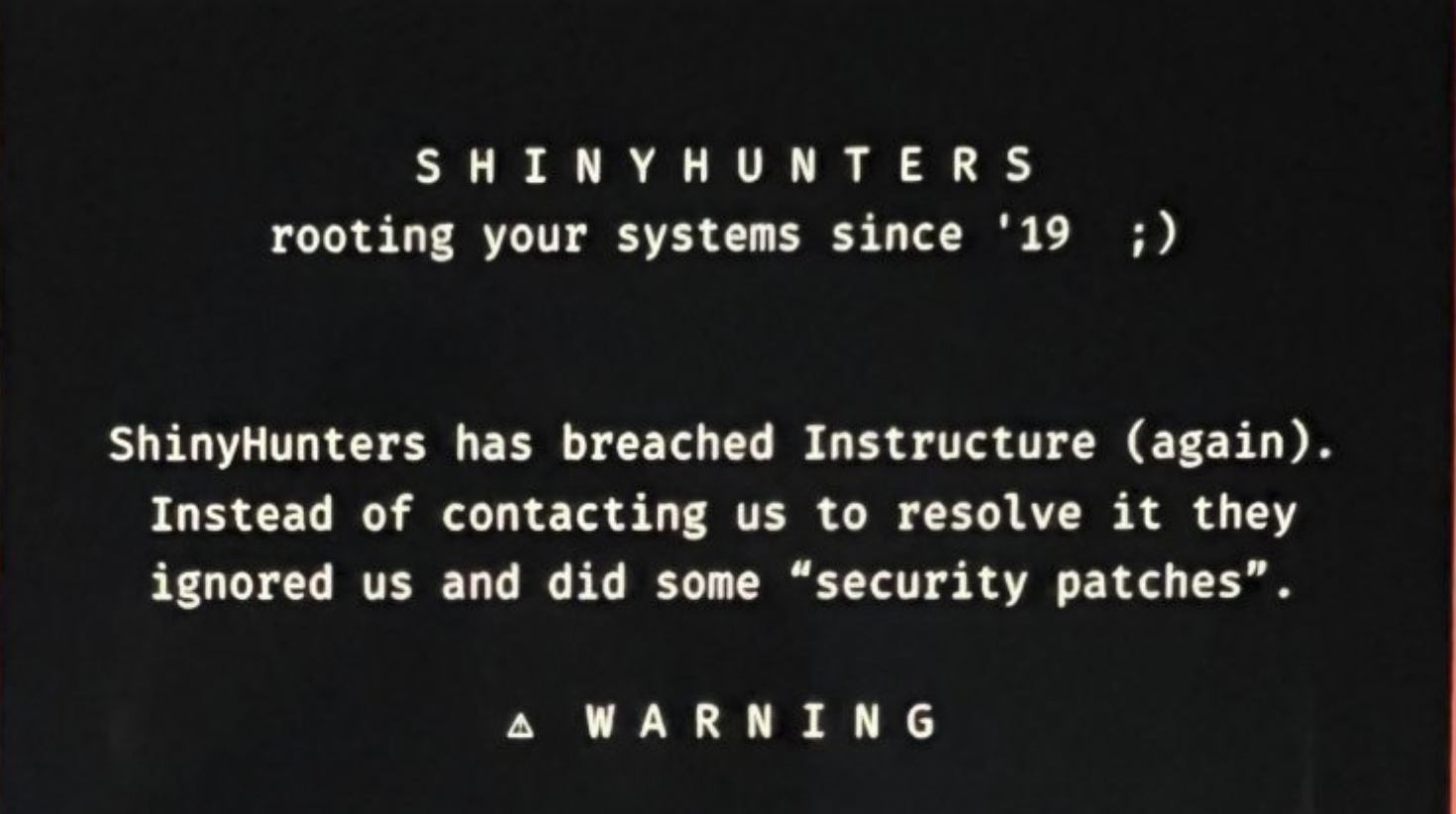
The cybercriminal group known as ShinyHunters has claimed responsibility for the attack. Reports indicate the breach may have exposed names, email addresses, student ID numbers, and billions of messages exchanged between students and faculty. Universities nationwide have reported disruptions, ransom notices, and unauthorized messages appearing inside Canvas portals during one of the busiest periods of the academic year: finals season.
Institutions reportedly impacted include universities such as University of Michigan, Michigan State University, Wayne State University, Pennsylvania State University, and University of Colorado Colorado Springs.
For education leaders, this incident should serve as a wake-up call.
A Third-Party Breach Does Not Mean Your University Is Safe
One of the most dangerous misconceptions in cybersecurity is the belief that a third-party breach somehow isolates risk away from the institution itself.
That is not reality.
Canvas may be a third-party platform, but universities and colleges remain deeply interconnected with these systems every single day. Learning management systems are tied directly into authentication services, email systems, cloud applications, student records, faculty communications, APIs, remote access services, and internal administrative processes.
When a trusted platform is compromised, attackers immediately begin looking for additional opportunities.
Who do you think they will come for next?
There is an enormous amount of valuable information stored within university infrastructures that cybercriminals want to exploit:
- Research data
- Student records
- Financial information
- Intellectual property
- Healthcare and medical research data
- Faculty communications
- Donor information
- Administrative systems
- Identity management infrastructure
Modern universities are some of the most complex digital environments in the world. Many operate thousands of endpoints across multiple campuses, cloud systems, remote learning platforms, public Wi-Fi environments, and decentralized IT operations. That complexity creates opportunity for attackers.
The Education Sector Is Under Attack
This is not an isolated incident.
Over the last 12 months, the education sector has experienced a sustained increase in cyberattacks targeting colleges, universities, and K-12 institutions nationwide.
The recent Canvas incident follows the major PowerSchool breach, another third-party education technology compromise that impacted schools across North America. The trend is becoming increasingly clear: attackers are focusing on centralized educational technology providers because one successful compromise can affect thousands of institutions simultaneously.
According to multiple 2026 cybersecurity threat intelligence reports, attackers are increasingly targeting:
- Cloud-based education platforms
- Identity and access management systems
- Public-facing applications
- APIs and integrations
- Remote access infrastructure
- Third-party vendors
- Student and faculty communication systems
Threat intelligence reporting throughout 2025 and 2026 also shows that ransomware and extortion groups continue evolving beyond simple encryption attacks. Today’s attackers steal sensitive data first, then threaten public exposure if organizations refuse to pay.
That is exactly what appears to be happening with the Canvas incident.
The reported extortion message associated with the attack warned institutions to “PAY OR LEAK.” This demonstrates a growing trend where cybercriminals weaponize operational disruption, reputational damage, and data exposure simultaneously.
Why Universities Must Prioritize Penetration Testing
I have personally spoken with IT Directors and CISOs at higher learning institutions who admitted that penetration testing has not been treated as a financial priority by university leadership.
That approach is becoming increasingly dangerous.
Penetration testing is no longer optional for colleges and universities.
Educational institutions cannot afford to assume their environments are secure simply because they have firewalls, antivirus software, or cloud-based services. Attackers only need one weakness to gain access.
A professional penetration test simulates real-world cyberattacks against an organization’s systems to identify vulnerabilities before threat actors exploit them.
For colleges and universities, penetration testing helps identify:
- Exposed systems
- Weak authentication controls
- MFA weaknesses
- Misconfigured cloud environments
- Vulnerable web applications
- API security gaps
- Privilege escalation paths
- Lateral movement opportunities
- Weak remote access controls
- Outdated software vulnerabilities
- Third-party integration risks
Most importantly, penetration testing helps institutions understand what an attacker could actually accomplish if they gained access to the environment.
That insight is critical.
The Risk Extends Beyond IT
University leadership must understand that cybersecurity incidents are no longer just IT problems. They are operational, financial, legal, and reputational crises.
The Canvas attack demonstrates this clearly.
Students preparing for finals suddenly lost access to coursework and assignments. Faculty faced disruptions to academic operations. Universities were forced into emergency response mode during one of the most sensitive periods of the academic calendar.
The consequences of a successful cyberattack can include:
- Operational shutdowns
- Delayed instruction
- Lost research data
- Ransom payments
- FERPA concerns
- Regulatory investigations
- Public relations damage
- Loss of student and parent trust
- Long-term financial impact
Many universities are already operating under financial pressure. Unfortunately, cybercriminals know this. They also know educational institutions often have limited cybersecurity staffing and inconsistent security maturity across campuses.
That makes higher education an attractive target.
The Future Threat to Higher Education
The implications of the current Canvas cyberattack could become far worse if university leadership continues treating cybersecurity as a secondary operational expense rather than a core institutional risk.
Artificial intelligence is also accelerating the threat landscape. Attackers are using AI-powered tools to automate reconnaissance, phishing campaigns, credential attacks, and vulnerability discovery at unprecedented scale.
At the same time, educational environments continue expanding:
- More cloud adoption
- More remote learning
- More connected applications
- More student devices
- More integrations
- More digital dependency
That means the attack surface continues growing every year.
The institutions that will fare best in this environment are the ones that proactively test their defenses before attackers do.
Universities Must Act Now
The Canvas breach should be a defining moment for education leadership across the United States.
Universities can no longer rely solely on vendors, internal assumptions, or compliance checklists to determine whether their environments are secure.
They must validate their security posture continuously.
Penetration testing provides leadership with real-world visibility into the weaknesses attackers are most likely to exploit. It helps institutions reduce ransomware risk, strengthen resilience, improve incident readiness, and protect the students, faculty, and communities that depend on them.
Cybercriminals are already targeting higher education aggressively. The next breach may not remain isolated to a third-party provider.
The next target could be the university itself.
To learn more about higher education penetration testing services, visit Firma IT Solutions or contact the team at 303-209-0386.